The concept of cloud computing broadly refers to the use of externally hosted IT resources online, and may relate to storage, hardware, and software. Cloud computing offers users access to computing resources from anywhere with instant scalability and fast deployment, resulting in widespread use by both businesses and individual users.
Cloud security covers the practices, principles, safeguards, and technologies that keep cloud data safe to use and help keep cloud infrastructures protected.
Cloud Computing Distinctions
Cloud security strategies are heavily dependent on the specific type of cloud technology in use. The four basic categories of cloud computing are:
- Public cloud services – These cloud infrastructures include infrastructure-as-a-service (IaaS), software as a service (SaaS), and platform-as-a-service (PaaS).
- Private cloud services from public cloud providers – These include personal cloud services delivered by third-party operators.
- Private cloud services run by internal staff – These solutions see internal teams running an architecture of virtual cloud systems under their control.
- Hybrid cloud services – These could be a combination of public and private cloud services for data management defined by cost, access, and security. They will be managed by internal teams in tandem with external cloud service providers.
Where previously most businesses’ IT policies would have seen data kept to a limited internal network, cloud computing requires data and operations to frequently be entrusted to third parties. Due to this, it’s vital to develop a close understanding of the security obligations that this confers upon your cloud computing practices.
Types of Cloud Security Solutions
Let’s take a look at a few key types of cloud security solutions and provides some examples for each:
| Type of Security Solution | Description | Use Cases |
| Identity and Access Management (IAM) | Controls who can access resources and services in the cloud. | Managing user permissions, ensuring only authorized users access sensitive data |
| Data Encryption | Protects data by converting it into a secure format. | Securing sensitive data in transit and at rest, compliance with data protection regulations |
| Intrusion Detection and Prevention Systems (IDPS) | Monitors and protects networks from malicious activity. | Detecting and responding to cyber attacks, preventing unauthorized access |
| Security Information and Event Management (SIEM) | Provides real-time analysis of security alerts generated by applications and network hardware. | Centralizing security event logging, identifying and responding to security incidents |
| Endpoint Security | Protects devices that access the cloud from security threats. | Securing laptops, mobile devices, and other endpoints accessing cloud services |
| Compliance Management | Ensures cloud environments meet industry standards and regulatory requirements. | Auditing and reporting for regulatory compliance, maintaining security standards |
| Data Loss Prevention (DLP) | Prevents unauthorized sharing or leakage of sensitive data. | Protecting sensitive information from being shared outside the organization, compliance with data privacy laws |
Division of Cloud Security Requirements
The vast majority of cloud service providers have proprietary security measures in place to ensure the integrity of their operations, as any cloud operator with a reputation for weak security will quickly lose its position in the market. However, due to the decentralized nature of cloud computing, these companies have little control over the circumstances regarding where and how their customers access their services.
Customers themselves can jeopardize the security of their cloud accounts through poor configuration, bad data management, and unsafe access habits. Each service type has its own definition of security that customers need to meet:
- Software-as-a-service – Customers are responsible for protecting their data and access.
- Platform-as-a-service – Customers are responsible for protecting data, access, and apps.
- Infrastructure-as-a-service – Customers are responsible for protecting data, user access, applications, operating software, and virtual network activity.
All public cloud services place some degree of responsibility on customers for protecting their data and designating access to their data. Without comprehensive data security, it’s impossible to truly leverage the benefits offered by the cloud. Companies that wish to adopt well-known SaaS products such as Salesforce or Microsoft Office need to first consider the measures that will be required to ensure that their organization is meeting its security responsibilities.
Similarly, businesses looking to acquire IaaS products like Microsoft Azure or Amazon Web Services will need a more considered security policy that also takes into account concerns over app security, network traffic, and operating software, as a greater number of services also multiplies the number of potential security vulnerabilities.
Cloud Security Concerns
Because public cloud services rely on third-party operations, particular challenges emerge when considering how to keep data safe during transmission to and from the cloud. These include:
- Cloud data visibility – Frequently, cloud services will be accessed from networks outside of a company’s immediate control by devices that the business doesn’t own, meaning that IT personnel need to be able to view activity on a cloud connection instead of monitoring traffic in a traditional internal network.
- Cloud data control – When dealing with third-party cloud solutions, IT staff don’t have the same degree of control that they would normally enjoy when managing local servers and applications. These limitations are inherent when using cloud services, and there’s no way for customers to access any physical IT hardware.
- Cloud data access – While customers can utilize applications and files online, configuring access permissions in the manner we usually describe is not possible. Users have the ability to access cloud infrastructure from any device with an internet connection, which has also led to the rise of bring-your-own-device (BYOD) solutions. The influence you will have over the security of access to these services is completely limited to the measures made available by your cloud provider, who’s staff also have the ability to override your own access.
- Cloud data compliance – Cloud computing services present organizations with additional challenges in the fields of compliance and regulation. Your cloud configurations may need to meet the regulatory standards of external bodies like PCI and HIPAA while also satisfying the expectations of internal departments, stakeholders, and customers. Any cloud solutions should also be implemented in accordance with the appropriate risk management procedures.
- Misconfiguration – Maintaining the integrity of cloud services’ security often falls to customers, particularly with regards to their configuration of the services. Research indicates that as little as 26% of companies utilitizing IaaS have the capacity for auditing these services for misconfiguration. Such errors frequently open the door for breaches in security of cloud services by allowing unauthorized access by outside parties. Research also shows that 99% of customers fail to detect configuration errors in their IaaS infrastructure.
- Cloud data recovery – Any internal cybersecurity strategy needs to provide contingency plans to mitigate against the effects of any breaches of cloud services. Such a contingency plan should provide processes and the appropriate resources to recover lost or compromised data to allow a company to function while shielding business from the greatest threats.
- Internal risks – While protecting a business from external breaches to cloud services should be paramount, it’s also worth safeguarding these solutions from the possibility of exploitation by rogue employees within the company. A recent Cloud Adoption and Risk paper published by McAfee suggests that as many as 85% of organizations show activity that could indicate internal security breaches.
Why is Cloud Security Vital?
Data security is a common concern among cloud customers, many of whom feel that their data would be at less risk when stored on local IT infrastructure. Ultimately, this is a misconception, since cloud providers generally offer a higher baseline of security measures and have a higher proportionate budget spend on security resources. Additionally, cloud storage shows better resiliency against viruses and other malware that can often breach the comparatively weaker security of local networks.
Maintaining the security of cloud storage is a matter of more than the proprietary measures put in place by cloud service providers. Customers themselves must take the necessary steps to protect access and ensure that the devices used to access the cloud do not reveal security vulnerabilities.
When selecting a cloud service provider, it’s vital to pick a business that prioritizes data security, and one that also mitigates against the risks posed by employee or IT error. As more and more cloud services integrate with public networks, the drawback is that the amount of potential vulnerabilities multiplies in kind. However, with the right security processes in place, customers can leverage the power of cloud computing with a minimum of risk.
Why Use Cloud Storage?
Everyday, more organizations are taking advantage of the benefit of cloud computing services over traditional local IT resources. Some of these reasons include:
- Cost – For most companies, cloud storage offers dynamic data storage infrastructure without the need for buying and maintaining a local server network.
- Resilience – Since data backed up on the cloud is dispersed around remote servers, it will remain safe in the event of a local threats like powercuts, building fires, and local malware attacks.
- Flexibility – Cloud storage services offer as much or as little storage as you need, relative to the real-time demands of your organization. This allows you to scale all your cloud computing with maximum efficiency.
- Ease of Access – Cloud services are available on any platform with a sufficient internet connection, allowing you to decentralize your IT infrastructure on a flexible ad-hoc basis.
How is Data in the Cloud Secured?
When you upload your data to the cloud, the provider will store multiple copies of it on different servers in geographically diverse locations. These server sites have cutting-edge fire suppression systems and backup power generation to ensure the safety of the servers from physical damage, along with other failsafes to protect data from employee error or malfeasance. At the customer’s point of access, authentication processes from login details like passwords and usernames along with features like two-step verification help maintain security.
In the middle lies the data tunnel between your device and the cloud provider’s servers. This presents another area of potential vulnerability against data breaches, but, fortunately, file encryption helps ensure security during this process. End-to-end encryption refers to the process of scrambling file information in transit between two devices, where the data is only reconstructed on the recipient’s device. This process is enabled by public-private encryption keys, often referred to as asymmetric cryptography.
The company’s cloud encryption software will use public keys to encrypt a file, but only the unique private key on a user’s device will be able to reconstruct the files. This helps maintain the most secure encrypted cloud storage, even in transit through networks that may not be completely secure. Not all cloud storage providers offer the highest levels of end-to-end encryption. However, there are alternative solutions that users can leverage to provide a layer of end-to-end encryption on whatever cloud service they want to use.
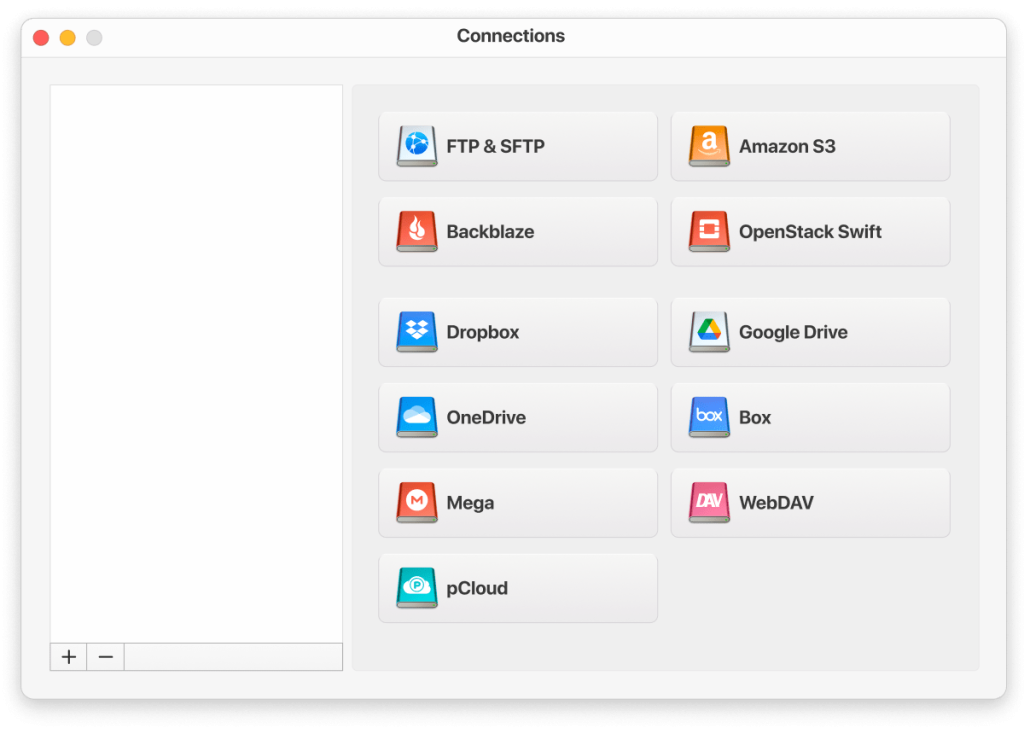
How to Boost Cloud Storage Security: CloudMounter
To ensure the safety of your cloud storage, users can choose a leading cloud storage manager like CloudMounter to provide the necessary layers of extra protection. CloudMounter boasts compatibility with all major cloud storage providers like Dropbox, Google Drive, Amazon S3, OpenStack Swift, Backblaze B2, MEGA, and more, along with protocols such as FTP, FTPS, SFTP, and WebDAV.
CloudMounter offers an intuitive “mounting” feature, whereby cloud storage accounts are presented just like local drives in Finder, allowing you to manage all your different cloud storage accounts through a single interface.
When it comes to security, CloudMounter also has you covered. The service employs AES-256 bit encryption for all your file transfer activity, providing top-notch protection at all times, no matter which cloud storage service you use. Just create a password on the storage, and the encryption key will be secured in the MacOS Keychain.
The result is that anyone who attempts to breach your files during transfer will only see garbled file information that can only be decrypted with your specific encryption key. The team behind CloudMounter are always hard at work on new ways to improve their offering, and the service will continue to update to keep itself compatible with the latest cloud storage solutions.
Basic Cyber Security Tips
Standard cybersecurity practices should not be neglected. So, if you want to maximize your security, follow this recommendations:
- Use strong passwords. If you use a combination of letters, numbers, and special characters, your password will be harder to crack.
- Protect your password manager. Make sure your password manager is protected by a strong master password.
- Back up your data regularly so that if the cloud fails, you can fully restore it.
- Change your access rights so that no single person or device can access all of your data unless required.
- Avoid accessing data over public Wi-Fi networks, especially if they don’t use strong authentication.
Conclusion
Due to its flexibility and ease of use, cloud storage offers multiple benefits to users over relying on traditional local storage when users can access their data anywhere and at any time from a smart device or laptop. But with more accounts accessed from different devices, the potential security threats start to mount up.
With CloudMounter, however, your files stay protected at every stage of the cloud storage process. Premium encryption measures combined with an intuitive file management interface allows users utilize cloud storage while keeping unauthorized access at bay. If you want to leverage the benefits of the cloud with peace of mind that all your files are secure and private, give CloudMounter a try.
Popular Articles
Frequently Asked Questions
Because cloud storage can be accessed from any browser or device connected to the internet, it opens users up to a greater risk of login details being stolen or accounts left logged in on different devices. Cloud storage security is also reliant on the network integrity of the internet connection you’re using to access your files.
As more users employ cloud storage, it becomes a bigger target for hackers. Hackers don’t necessarily have to penetrate the cloud storage security itself for your data to become compromised – it only takes one of your devices to get hacked for cybercriminals to have your login details, as many stories of high profile data leaks make clear.
The major cloud providers generally boast the best security. Google Drive security is arguably the gold standard for cloud storage services, but Dropbox security and Amazon S3 are also comprehensive.