Cloud encryption is the process through which the data is transformed and encoded while it’s stored or transferred in a cloud service. Through mathematical algorithms, the plaintext data is converted into ciphertext that makes the files unreadable by unauthorized users who may gain access without permission.
Throughout this article, we’re defining cloud encryption and explaining its importance, as well as some of the best practices in the domain for 2026.
Defining Cloud Encryption
File encryption is a process offered by most cloud storage providers that enhances data storage security and keeps the uploaded files safe even in the rare events of data breaches by unauthorized users. It’s achieved through several algorithms and protocols like HTTPS, SSL, or FTP.
The best cloud encryption services provided by cloud storage vendors need to be in compliance and meet the regulatory standards of numerous institutions like the Federal Information Processing Standards or the Federal Information Security Modernization Act.
How Does Cloud Encryption Work?
Encryption secures data by transforming it into a format that is unreadable without the correct key. Authorized users with the key can decrypt the data, making it accessible only to them. Access to these keys is restricted to verified and trustworthy individuals, who are authenticated through multiple security steps.
In the context of cloud services, encryption safeguards data both while it is being transmitted to and from cloud applications (data in transit) and while it is stored on the cloud servers (data at rest).
Cloud Encryption Importance in 2026
In the digital era data protection and safety is crucial. For many companies it’s the key to success and cloud storage services are always innovating to provide the best features. Not only is it vital to keep your private data safe for commercial reasons, but unauthorized access can lead to serious difficulties for any company or individual that relies on cloud services.
With so many cybersecurity threats out there, knowing that your cloud data is untouchable gives you the peace of mind needed to focus on other aspects of your activity. We’re analyzing a few of the most important aspects related to cloud encryption and the role it plays in 2026.
Ensures 24/7 Data Protection
As stated in the introduction, knowing that every file and folder uploaded on the cloud is in safe hands at all times allows you to focus on more pressing issues. Furthermore, since information is power, you can rest assured knowing that the competition can’t peek into your strategies or plans. In other words, it makes data management a lot easier and it doesn’t require any extra steps from the user as the cloud storage provider handles the encryption.
Mitigates Insider Threat
Besides keeping cybercriminals and the competition away from your data, cloud encryption is also extremely helpful for mitigating insider threats. Running a business is hard enough without worrying about employees selling sensitive data or engaging in cyber vandalism. Furthermore, insider threats can take the form of accidental breaches so encryption is the only way of making sure everything is secure. Besides cloud encryption, using software to disable removable storage or crawl email attachments is also a good way to keep your data safe.
Overcomes Insecure APIs
You can’t really build a successful business in the digital environment without using APIs. However, API security can feel complicated at times and it can even lead to security breaches. That’s where cloud encryption comes in. Even if your IT team used an insecure API, that extra layer of protection makes sure your organization, customer data, and user profiles are out of harm’s way.
Maintains Organizational Integrity
Companies rely more and more on cloud storage for their operations and, besides the improved speed and security, these services are beneficial for organizational integrity as well. Encrypted data is a lot harder to manipulate or alter and even if it does happen, it’s quite easy to detect such actions.
Ensures Protection for Multiple Devices
Opposed to local encryption, cloud services guarantee the same protection levels on multiple devices. In other words, it allows companies to save a lot of resources that would be used to secure the various devices. So, even if a compromised device is used to access cloud data, there’s no risk involved.
Guarantees Compliance
Another one of the many benefits brought by cloud encryption is ensuring compliance with various regulators and standards. No matter if we’re referring to FIPS, HIPPA, or GDPR, there are lots of regulations on how data should be stored and encrypted. Choosing a cloud encryption system guarantees your compliance without extra work.
Types of Cloud Encryption
There are several different types of cloud encryption. Each type has unique characteristics and uses. Let’s take a look at some of them:
| Encryption Type | Description | Use Cases |
| Server-Side Encryption (SSE) | Encryption performed by the cloud service provider before storing data on their servers. | Data at rest in cloud storage (e.g., AWS S3, Google Cloud Storage) |
| Client-Side Encryption | Encryption performed by the client before uploading data to the cloud. | Sensitive data that needs to be encrypted before it leaves the client’s environment (e.g., files on personal devices) |
| End-to-End Encryption | Encryption where data is encrypted on the sender’s side and only decrypted on the receiver’s side, without intermediate decryption. | Messaging apps (e.g., Signal, WhatsApp) |
| Homomorphic Encryption | Allows computation on encrypted data without decrypting it, producing encrypted results. | Secure data processing and analysis in the cloud without exposing raw data (e.g., healthcare data analysis) |
| File-Level Encryption | Encryption applied to individual files before they are uploaded to the cloud. | Protection of individual files (e.g., sensitive documents) |
Best Practices in Cloud Encryption
When it comes to cloud encryption, there’s no predefined way to make sure everything is handled. It’s a different scenario from one organization to the other and the security team should be responsible for mapping out the requirements for stored, in use, and in-transit data.
Establishing the best encryption layer for cloud data starts with deciding the following:
- What data needs to be encrypted – based on internal classification and compliance requirements.
- When the encryption is needed – in use, at rest, and in transit.
- Who hold the encryption keys – it’s either the enterprise or the cloud service provider.
Based on these three action points, we can formulate some of the best practices when encrypting data. First of all, all the in transit data has to be encrypted if it leaves the internal network. No matter the external destination, it will surely pass through numerous third parties and encryption is mandatory. The most common solution for encrypting in transit data is the file Transfer Protocol. However, using VPNs and IP security can be used to improve data protection as well.
All sensitive data should be encrypted both when in use and at rest. Furthermore, it should be backed up before the upload. This level of protection is achieved through full memory and drive encryption. However, this system could prevent certain applications from processing the data.
Last but not least, encryption key management is vital for the overall process. It goes without saying that the keys should always be stored separately from encrypted data and off site backups are also mandatory. A multifactor authentication system for the master and recovery keys is recommended as well.
Get Top Level Cloud Encryption with CloudMounter
No matter the cloud storage account you opt for, there’s no such thing as too much protection. CloudMounter adds an extra encryption layer on top of what’s provided by the cloud storage service. This means that even if someone manages to breach the cloud security systems, CloudMounter will keep all your data safe through its built-in AES-256 algorithm. So, even if someone gets access to your cloud files, they won’t be able to read or access them as only you have the decryption key.
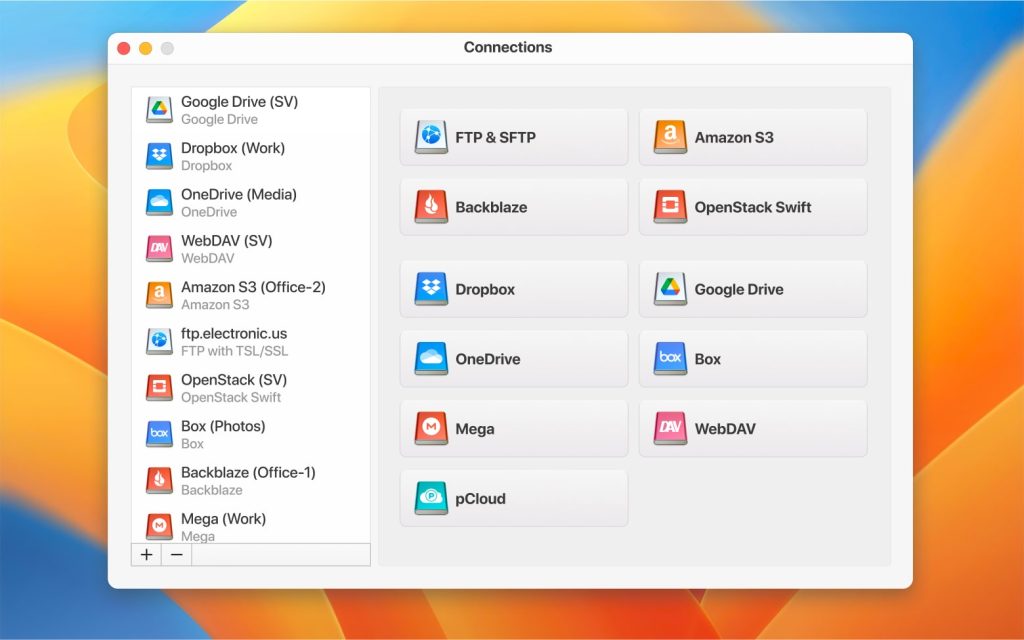
Using CloudMounter to set up the encryption is straightforward and doesn’t require advanced computer knowledge. Simply activate the encryption feature, set a password, and safely store it in Keychain.
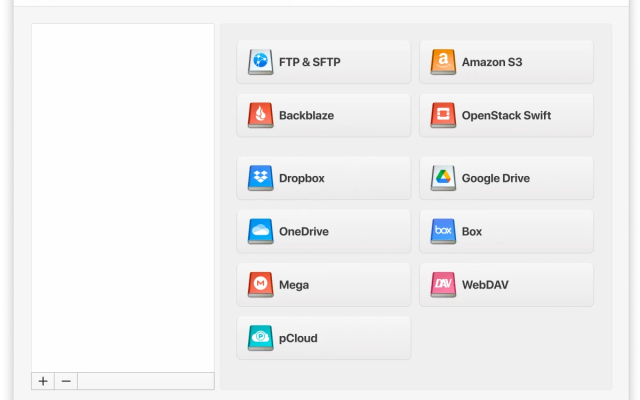
Besides providing top-grade encryption for your online data, CloudMounter comes with several other advantages as well. It allows you to mount the most popular cloud storage services like Google Drive, Amazon S3, OneDrive, or Dropbox, as local drives. So, you’re getting extra protection and a facile way to manage data as it would be stored on your computer. Thanks to the Finder integration, CloudMounter makes it very easy to locate any files you need and perform a wide range of tasks.
Final Thoughts
There’s no shortage of challenges when it comes to protecting cloud-stored data. However, you now have the knowledge and tools needed to keep your files safe. And while the enterprise cloud service providers deliver great protection, the best approach is to add an extra layer through CloudMounter. Besides an upgraded cloud security, the software enables you to mount multiple cloud accounts simultaneously so you also save time managing the online data.
Popular Articles
Frequently Asked Questions
Since homomorphic encryption allows users to use the encrypted data without first decrypting it, it’s one of the most popular methods used by cloud storage services. It’s faster and it allows data to be outsourced while maintaining its encrypted status.
The major cloud services like Google Drive, Amazon S3, or OneDrive don’t apply end-to-end encryption on their platforms. It’s believed to come with potential security flaws and homomorphic encryption is preferred. However, services like MEGA, Sync.com, or Tresorit are a few examples of cloud services using end-to-end encryption.
Data encryption in cloud computing is the process through which all the files stored in the cloud are transformed to ciphertext so even if there’s a data breach, the contents can’t be used. The efficiency of cloud computing relies on data encryption.